Your cryptocurrency is only as secure as the steps you take to protect it. Unlike traditional banks, there’s no safety net if your funds are stolen or lost. Blockchain technology is secure, but cybercriminals exploit weaknesses in how wallets and private keys are managed. Here’s what you need to know:
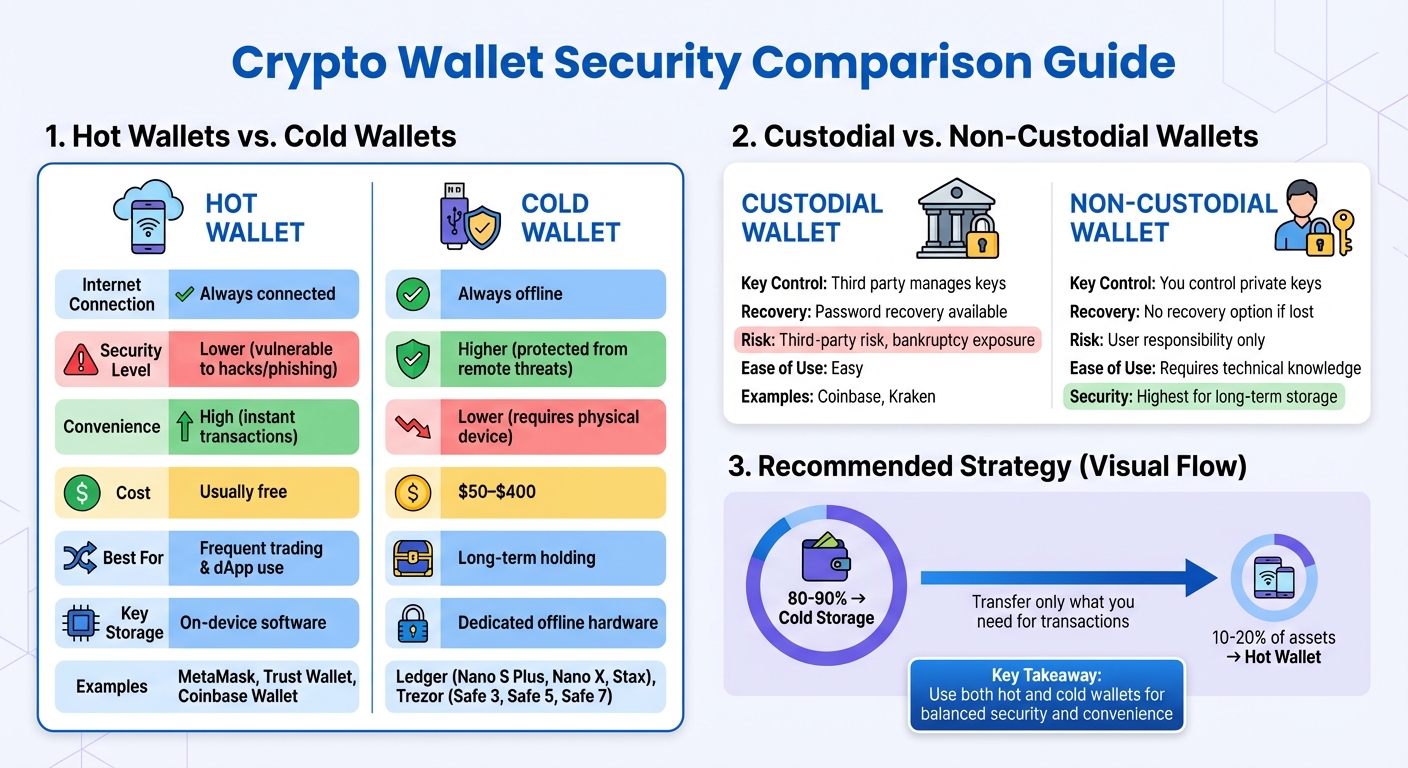
- Wallet Choice Matters: Hot wallets (online) are convenient but less secure. Cold wallets (offline hardware) offer higher security for long-term storage. Use both for a balanced approach.
- Private Key Control: Non-custodial wallets give you full control but require careful management of keys and seed phrases. Custodial wallets are easier to use but come with third-party risks.
- Basic Security Practices: Use strong, unique passwords stored in a password manager. Enable multi-factor authentication (MFA), preferably with hardware keys.
- Advanced Strategies: Regularly update wallet software, revoke unused smart contract permissions, and divide assets across multiple wallets to reduce risk.
- Transaction Safety: Avoid public Wi-Fi, verify recipient addresses carefully, and stay alert to phishing attempts.
Key takeaway: A layered security approach is essential. Use hardware wallets for critical assets, back up seed phrases securely, and stay vigilant against evolving threats.
Types of Crypto Wallets and Their Security Features
Crypto Wallet Types Comparison: Security Features and Use Cases
Choosing the right crypto wallet is all about finding the right balance between security and convenience. Each type of wallet comes with its own set of pros and cons, so understanding these differences can help you protect your assets while maintaining the access you need.
Hot Wallets vs. Cold Wallets
When it comes to wallet connectivity, the distinction between hot and cold wallets is crucial for managing risk. Hot wallets are software-based and remain connected to the internet, making them ideal for quick transactions and interacting with decentralized apps (dApps). Popular options include MetaMask, Trust Wallet, and Coinbase Wallet, all of which are free to download and use.
Cold wallets, however, operate entirely offline. These are often hardware devices designed to store your private keys securely. Gaurav Roy from Ledger Academy puts it simply:
a cold wallet is a type of crypto wallet that never interacts with any smart contracts.
This offline setup shields cold wallets from phishing attempts and remote attacks. By generating and storing keys offline, they minimize exposure to online risks.
| Feature | Hot Wallet | Cold Wallet |
|---|---|---|
| Internet Connection | Always connected | Always offline |
| Security Level | Lower (vulnerable to hacks/phishing) | Higher (protected from remote threats) |
| Convenience | High (instant transactions) | Lower (requires physical device) |
| Cost | Usually free | $50–$400 |
| Best For | Frequent trading & dApp use | Long-term holding |
| Key Storage | On-device software | Dedicated offline hardware |
Many investors find that a hybrid approach works best. You can use a hot wallet for day-to-day transactions while keeping the majority of your assets in a cold wallet for long-term storage. When you need to make a transaction, simply transfer the necessary amount from your cold wallet to your hot wallet, then move any unused funds back to cold storage.
Custodial Wallets vs. Non-Custodial Wallets
The main difference here lies in who controls your private keys. Custodial wallets put a third party in charge of key management, while non-custodial wallets give you full control – but also full responsibility.
Custodial wallets are often tied to exchanges like Coinbase or Kraken. These services manage your keys and even offer password recovery. However, relying on a third party introduces risks. For example, Coinbase warned in a May 2022 SEC filing:
…because custodially held crypto assets may be considered to be the property of a bankruptcy estate, in the event of a bankruptcy, the crypto assets we hold in custody on behalf of our customers could be subject to bankruptcy proceedings and such customers could be treated as our general unsecured creditors.
Non-custodial wallets, on the other hand, put you in the driver’s seat. You hold your private keys and seed phrases, eliminating third-party risk. However, this also means there’s no safety net – if you lose your seed phrase or forget your password, your funds are gone for good. For long-term asset protection, non-custodial cold storage using hardware wallets is often considered the safest option.
Hardware Wallets for Maximum Security
If security is your top priority, hardware wallets are the way to go. These devices store your private keys offline and require physical confirmation for every transaction. They’re about the size of a USB drive and are designed to keep your keys secure at all times. Popular models include Ledger (Nano S Plus, Nano X, Stax) and Trezor (Safe 3, Safe 5, Safe 7).
Here’s how they work: when you initiate a transaction on your computer or phone, the transaction details are sent to your hardware wallet. The wallet then signs the transaction internally using your private key. As Trezor explains:
The private key itself never leaves the hardware wallet, so it remains secure throughout the process.
Only the signed transaction is sent back, ensuring your private key never leaves the device.
To add an extra layer of protection, hardware wallets require physical confirmation, such as pressing a button or using a touchscreen, for every transaction. Even if your computer is compromised, your private keys remain safe. Many devices also include PIN protection. For example, Trezor wallets automatically erase data after 16 failed PIN attempts, and some models allow PINs up to 50 digits long.
Modern hardware wallets come with advanced features like touchscreens (e.g., the Trezor Safe 7 with its 2.5" display) and wireless charging, while supporting thousands of cryptocurrencies. These features make them a robust choice for safeguarding your digital assets.
Up next, we’ll cover basic security practices to help you further protect your crypto holdings.
sbb-itb-39d39a6
Basic Security Practices for Crypto Assets
Once you’ve chosen a wallet that suits your needs, the next step is to establish strong security habits. These practices are your best defense against theft, hacking, or accidental loss.
Creating and Managing Strong Passwords
Your password is the gateway to your crypto assets, so it needs to be robust. Aim for a password that’s at least 16 characters long, combining uppercase and lowercase letters, numbers, and special characters. Avoid predictable patterns, like common words or sequential numbers – hackers can crack these with ease.
With non-custodial wallets, the stakes are even higher. There’s no "forgot password" option or help desk to retrieve lost credentials. If you lose your password, your funds are permanently inaccessible.
To manage this, use a trusted password manager to generate and safely store unique, complex passwords for all your accounts. Never reuse passwords, especially for critical services like email, banking, or crypto platforms. For additional security, keep a physical copy of your password in a fireproof safe or a bank safe-deposit box. If you’re using a mobile wallet, enabling biometric authentication (like fingerprint or facial recognition) adds an extra layer of protection.
Once your password is secure, it’s time to add another layer of defense: multi-factor authentication.
Setting Up Multi-Factor Authentication (MFA)
Even the strongest password can be compromised, which is where multi-factor authentication (MFA) comes in. MFA adds a second layer of verification, making unauthorized access much more difficult .
However, not all MFA methods are equally secure. SMS-based two-factor authentication is the least secure option because it can be bypassed through SIM swapping, where attackers hijack your phone number. A better choice is an authenticator app like Google Authenticator or Authy, which generates time-sensitive codes that refresh every 30 seconds. For the highest level of security, consider a hardware security key like YubiKey. These keys require physical possession to authorize any action, making them far more secure.
| Authentication Method | Security Level | Main Vulnerability |
|---|---|---|
| SMS / Email 2FA | Low | SIM swapping, phishing |
| Authenticator Apps | Medium | Malware compromise |
| Hardware Keys (YubiKey) | High | Physical theft |
For devices that support built-in MFA, these can work seamlessly alongside other security measures, providing added convenience and protection.
Protecting Private Keys and Seed Phrases
Your private keys and seed phrases are the foundation of your crypto security. A seed phrase – typically 12 to 24 random words – acts as the master key to your wallet. If someone gains access to it, they can control your funds. And if you lose it without a backup, your assets are gone for good.
Never store your seed phrase digitally. This means no typing it into computers, phones, or cloud storage. Avoid taking screenshots or saving it in apps like Notes or cloud services such as Google Drive. As Trezor advises:
Trezor will NEVER ask you to enter your wallet backup digitally (except on your Trezor device if you choose to verify it).
Write your seed phrase on paper as soon as it’s generated and store it securely in a fireproof safe or a bank safe-deposit box. To protect against fire or water damage, consider engraving it onto titanium or steel plates, which are far more durable .
For an added layer of security, distribute your seed phrase across multiple locations. For example, keep one copy in a home safe and another in a bank safe-deposit box. To ensure your backup remains functional, perform a quarterly recovery test by using your seed phrase to verify access to a small amount of crypto on a second device. This simple check can save you from future headaches.
Advanced Security Strategies for Digital Assets
Building on basic security measures, these advanced strategies help shield your digital assets from increasingly sophisticated threats.
Dividing Assets Across Multiple Wallets
Spreading your crypto holdings across multiple wallets adds an extra layer of protection. By doing this, you reduce the risk of losing everything if one wallet is compromised. Security experts suggest storing 80–90% of your assets in cold storage for long-term safekeeping, while keeping only 10–20% in hot wallets for active trading or transactions. While managing several wallets may seem more complex, it eliminates the danger of relying on a single point of failure. This approach works alongside your foundational security practices to minimize potential losses.
Keeping Wallet Software Updated
Using outdated software is like leaving your front door unlocked – it makes you an easy target for hackers. Regular updates fix vulnerabilities and ensure compatibility with the latest blockchain advancements. This applies to your device’s operating system, browsers, and hardware wallet firmware.
"Security isn’t static, and failing to update your firmware could mean your device doesn’t include the latest updates to keep your assets safe." – Ledger
To stay safe, always download updates directly from official manufacturer websites or verified app stores. Avoid clicking on links from sponsored ads or emails, as these could lead to malicious sites. A 2025 FBI report highlighted malware that exploited outdated wallet software, emphasizing the critical need for timely updates. For hardware wallets, check for firmware updates at least every three months. If you use software wallets, enable automatic updates whenever possible.
Revoking Smart Contract Approvals
When you use decentralized applications (dApps), you often grant them permission to access your tokens. These permissions can pose a risk if left active – if the dApp is hacked or has vulnerabilities, attackers could exploit these approvals to steal your funds. This is a common tactic used by wallet-draining malware.
To protect yourself, disconnect your wallet from a dApp as soon as you’re done with your transactions. Regularly review your active permissions and revoke any that are no longer necessary. Including this step in your routine wallet audits significantly reduces the risk of platform-specific attacks. It’s a small but crucial habit that strengthens your overall security strategy.
Security Measures for Crypto Transactions
Having a secure wallet is only part of the equation when it comes to protecting your crypto assets. Transactions themselves are often where vulnerabilities arise, whether from network attacks or human error. To ensure your crypto remains safe, it’s essential to follow these key practices to guard against common threats.
Avoiding Public Wi-Fi and Using VPNs
Public Wi-Fi networks – like those at coffee shops, airports, or hotels – can leave your crypto transactions exposed. Hackers can use techniques like man-in-the-middle attacks to intercept sensitive data, putting your funds at risk. For this reason, avoid conducting any crypto-related activity over public Wi-Fi.
If you must access your wallet while on the move, a premium Virtual Private Network (VPN) is a safer option. Look for a VPN with a "Kill Switch" feature, which ensures your IP address isn’t exposed if the connection drops. Many premium VPN services also offer free trials, making them accessible when needed.
Verifying Transaction Details
Blockchain transactions are irreversible, meaning that sending crypto to the wrong address results in permanent loss. Malware can even tamper with wallet addresses displayed on your device, so it’s crucial to double-check the recipient’s address. Use the secure display on your hardware wallet to verify the address, and for high-value transfers, confirm the details through a secondary method, such as a phone call, text, or in-person verification.
A stark reminder of the importance of vigilance is the Bybit exchange incident in February 2025, where $1.4 billion was lost due to malicious code that tricked staff into approving fraudulent transactions. To reduce risks, consider using hardware wallets equipped with "Clear Signing" features. These devices display transaction details in plain text, allowing you to review and confirm all information before proceeding .
Recognizing and Avoiding Phishing Attacks
Phishing remains one of the most significant threats to crypto holders. In just the first half of 2025, phishing and wallet compromises accounted for $3.1 billion in losses. Scammers have become increasingly sophisticated, with deepfake voice phishing attacks rising by an alarming 1,633% during Q1 2025.
To protect yourself, never click on unsolicited links claiming to be from wallet providers or exchanges. Instead, manually type the official website address into your browser to avoid falling for fake clones . Check that the website uses HTTPS and that the URL matches the official name exactly – scammers often create look-alike domains with minor differences .
Be cautious of urgent alerts about account issues, unrealistically lucrative offers, or requests for private keys or seed phrases. Legitimate companies will never ask for this kind of sensitive information. For added security, make use of whitelisting features offered by many exchanges. These allow you to pre-approve wallet addresses, ensuring that funds can only be sent to verified destinations.
Conclusion
Protecting your cryptocurrency requires multiple layers of security – there’s no single solution that can protect against every potential threat. While the blockchain itself is incredibly secure, the real risks come from how you access and manage your wallets. By combining the right strategies, you can significantly reduce your exposure to these risks.
A balanced approach works best. Use hot wallets for smaller, everyday transactions, and store the majority of your holdings in cold storage for long-term safety. As Johnny Gabriele, Head Analyst of Blockchain Economics and AI Integration at The Lifted Initiative, wisely puts it:
I always tell people to treat their hot wallet like they would their actual wallet – never store more than you’d be okay losing.
Since cryptocurrency transactions are permanent, there’s no room for error. Stories of investors losing millions due to forgotten passwords serve as a stark reminder of how crucial it is to act on these security measures now.
Securing your crypto isn’t something you set up once and forget. It’s an ongoing responsibility. Update your wallet software regularly, revoke permissions for unused smart contracts, and test your recovery plans. As Alex Carchidi, author at Quantum Canary, points out:
The question is less ‘can you remove all risk’ and more ‘can your habits match the threats you actually face’.
Take action today. Back up your seed phrases on physical media and store them in multiple secure locations. Enable hardware-based two-factor authentication, set up a clear inheritance plan, and conduct regular security audits. The safety of your digital assets depends entirely on the choices you make right now.
FAQs
What’s the difference between hot and cold wallets when it comes to security?
The main distinction between hot wallets and cold wallets comes down to their internet connection and security features. Hot wallets are always online, which makes them perfect for frequent transactions. But this constant connection also exposes them to risks like hacking and phishing.
On the other hand, cold wallets keep your private keys offline, offering a higher level of protection. Without an internet connection, they’re much harder for cybercriminals to target. This makes cold wallets a great option for storing cryptocurrency over the long term. The trade-off? They’re less convenient for everyday use since accessing your funds requires extra steps.
What are the best ways to securely store and protect my private keys and seed phrases?
To protect your private keys and seed phrases, steer clear of storing them on devices connected to the internet. These devices are susceptible to hacking, malware, and phishing attacks. A safer option is to store them offline, either in a hardware wallet or on a sturdy physical medium like paper or metal. Hardware wallets, such as Ledger or Trezor, are particularly reliable because they keep your private keys offline, greatly reducing exposure to online threats.
For added security, place your seed phrase in a secure spot, like a safe or a safety deposit box, and avoid creating digital backups or using cloud storage. Never share your private keys or seed phrases with anyone, and stay vigilant against phishing scams aiming to steal this sensitive information. Regularly update your hardware wallet’s firmware and think about using multi-signature authentication for an extra layer of protection. These precautions can help safeguard your digital assets from theft or hacking.
What are the best ways to secure my cryptocurrency from hackers and cyber threats?
To keep your cryptocurrency safe from hackers and cyber threats, start with a hardware wallet like Ledger or Trezor. These devices store your private keys offline, making it much harder for hackers or malware to access them.
Next, consider using multi-signature authentication. This feature requires multiple approvals before any transaction can go through, adding an extra layer of protection against unauthorized access. It’s also crucial to store your private keys securely in an offline location – whether that’s a hardware wallet or even a paper wallet stored in a safe spot.
Don’t forget to enable two-factor authentication (2FA) on your accounts for an added security boost. Regularly updating your wallet software is another must – it ensures you’re protected against any newly discovered vulnerabilities. Lastly, always stay vigilant for phishing scams, as they remain a common way for attackers to steal digital assets. By combining these steps, you can better protect your cryptocurrency and reduce the risks of cyber threats.

